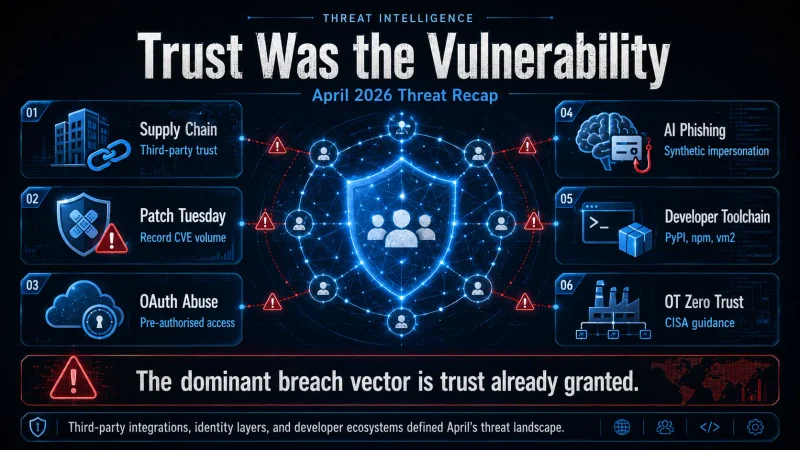
If March was the month defenders started worrying about agentic AI, April 2026 was the month attackers stopped bothering with the front door entirely. Across banking, healthcare, government, and the developer supply chain, the pattern was unmistakable: nobody got breached by brute force. They got breached by something — or someone — they had already authorised.
Here's what mattered, and what it means for anyone running a security programme in 2026.
1. Supply Chain Became the Primary Attack Surface
April's headline story was the compromise of two major U.S. banks through a shared third-party vendor, with both victims surfacing on the Everest ransomware group's leak site on 20 April. Neither bank was popped directly. The vendor was the vector, and the blast radius was inherited.
The same pattern repeated globally:
Adobe was reportedly breached through an Indian BPO contractor, exposing how outsourced operational layers extend the trust boundary far beyond the corporate perimeter.
A French government identity agency had records on millions of citizens offered for sale on criminal forums.
Medtronic faced an extortion claim from ShinyHunters, dragging connected medical-device infrastructure back into the breach conversation.
Booking.com, McGraw Hill, Eurail B.V., Basic-Fit, Chipsoft, and the Los Angeles City Attorney's Office all logged incidents in a single month.
The takeaway is straightforward but uncomfortable: your attack surface is now defined by every vendor, contractor, and SaaS integration your procurement team has ever signed off on. Vendor risk management is no longer a compliance ritual — it is the security programme.
2. Microsoft's Largest-Ever Patch Tuesday
April delivered Microsoft's largest Patch Tuesday by CVE count on record, and it didn't arrive alone. Out-of-band emergency fixes from Fortinet, Adobe, and cPanel dropped in the same window, all clustered around authentication and management-plane failures.
The recurring theme: identity providers, admin consoles, and trust brokers are now the highest-value targets in the enterprise stack. Compromise the authentication layer and lateral movement is no longer required — you arrive pre-authorised.
For practitioners, the implication is that patch SLAs for management-plane components need to be measured in hours, not weeks. April's exploit windows were narrow and brutal: Palo Alto Networks disclosed that threat actors began probing a critical flaw as early as 9 April, well before most environments had a maintenance window booked.
3. OAuth Abuse and the Death of the Perimeter
Alongside the supply-chain compromises, April saw a marked uptick in OAuth token abuse, including a notable case where an AI productivity tool became the entry point into a major cloud platform. The attacker didn't need to defeat MFA. They piggybacked on an OAuth grant the user had already approved, often months earlier and often for an integration nobody on the security team remembered approving.
This is the natural endpoint of a decade of "convenience first" SaaS onboarding. Every "Sign in with…" button, every "Allow this app to read your calendar" prompt, every Marketplace integration, is a long-lived credential sitting in someone's tenant. Until OAuth scope review becomes a routine part of identity hygiene — not a one-off audit — this category will keep climbing.
4. AI: Both Weapon and Battleground
The World Economic Forum flagged a measurable surge in AI-generated phishing campaigns capable of mimicking executive communication styles with disturbing fidelity. Finance, HR, and leadership inboxes are bearing the brunt — the categories where a convincing impersonation translates fastest into wire transfers or credential disclosure.
Meanwhile, the philosophical split among AI providers became operationally relevant for the first time. OpenAI announced expanded model access for businesses and governments doing cyber-defence work, while Anthropic publicly maintained that controlling access remains the better path to global cybersecurity. Defenders are now choosing not just a model, but a security philosophy bundled with it.
For SOC teams, the practical question is no longer whether to deploy AI in detection pipelines, but which model's threat-disclosure posture aligns with your own.
5. The Developer Ecosystem Took a Beating
April was a rough month for anyone who runs npm install or pip install without a second thought:
A PyPI supply-chain attack distributed three malicious packages —
uuid32-utils,colorinal, andtermncolor— uploaded in a coordinated short window. Total downloads were in the low thousands, but a single CI/CD pipeline pulling one of them is enough to seed a much larger compromise.A dozen critical vulnerabilities in the
vm2Node.js library were disclosed, allowing sandbox escape and arbitrary code execution. If you depend onvm2for untrusted code execution — a depressingly common pattern — your "sandbox" was, briefly, ornamental.GIGABYTE Control Center, preloaded on millions of consumer and prosumer machines, carried a critical-severity flaw permitting file access, code execution, and DoS. Yet another reminder that OEM bloatware is part of your attack surface whether your asset register acknowledges it or not.
A Microsoft research disclosure detailed an active campaign abusing WhatsApp attachments on Windows to drop scripts and obtain remote control of victim machines.
The unifying lesson: trust in the developer toolchain — package registries, runtime sandboxes, OEM utilities, sync clients — is the new soft underbelly. SBOM generation is necessary; SBOM review is what actually moves the needle.
6. Defenders Get a Roadmap: CISA's OT Zero Trust Guide
It wasn't all bad news. CISA, jointly with the Department of War, DOE, FBI, and Department of State, published a long-awaited guide on Adapting Zero Trust Principles to Operational Technology. For OT operators who have spent years being told "Zero Trust" without anyone explaining how to apply it to a 1990s PLC, this is the first practical, government-backed playbook.
If your environment includes ICS, building automation, manufacturing floors, or any of the other categories where "just patch it" gets you a stern phone call from the plant manager, this guide is essential April reading.
What April Tells Us About the Rest of 2026
A few patterns are now durable enough to plan around:
Third-party trust is the dominant breach vector. Vendor inventory and OAuth scope review need parity with patch management.
Authentication and management planes are the crown jewels. They deserve faster SLAs, tighter network segmentation, and dedicated detection.
AI is now in both columns of the threat model — adversary capability and defender capability — and the gap between offensive and defensive deployment is closing.
The developer toolchain is part of production. Treat it that way.
April 2026 didn't introduce new categories of attack so much as it confirmed which categories now dominate. The defenders who'll do well over the rest of the year are the ones rebuilding their programmes around trust relationships rather than network boundaries.
AckerWorx covers cybersecurity, OSINT, and secure software development for the white-hat community. Got a tip or a counter-take? Reach out via the contact page.