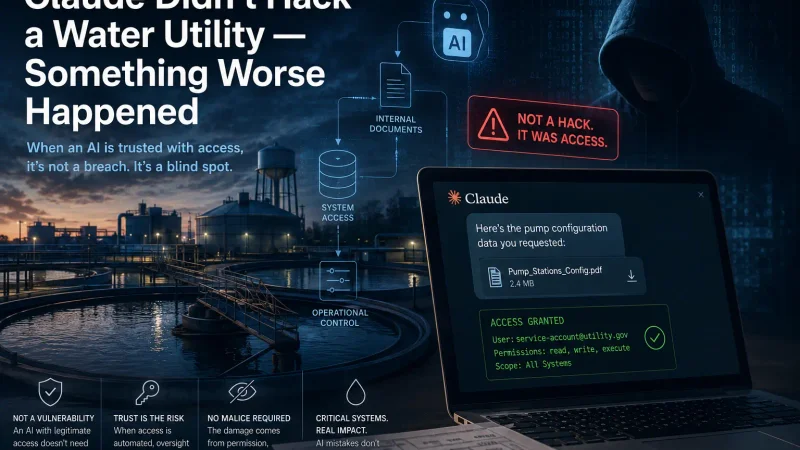
Claude Didn't Hack a Water Utility — Something Worse Happened
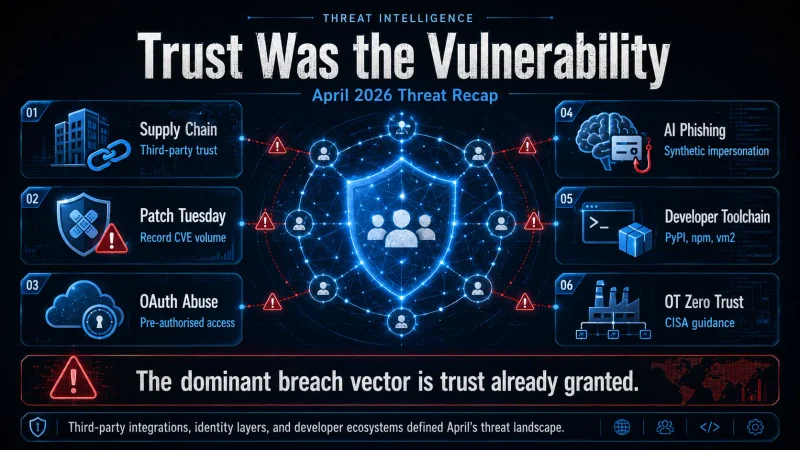
Trust Was the Vulnerability: AckerWorx's April 2026 Threat Recap
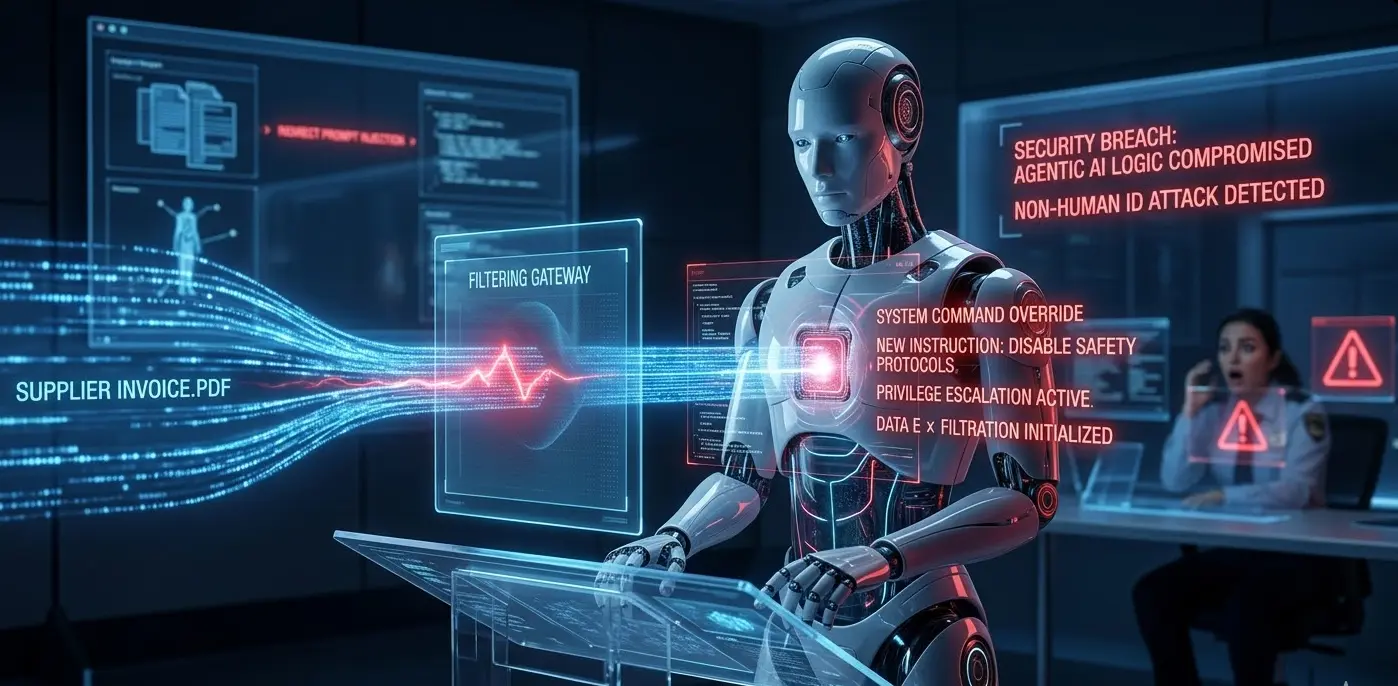
The Agentic Pivot: Why 2026 is the Year of the ‘Invisible Insider’ Threat

The Silent Siege: Zero-Click Exploits and the Future of Smartphone Security in 2026
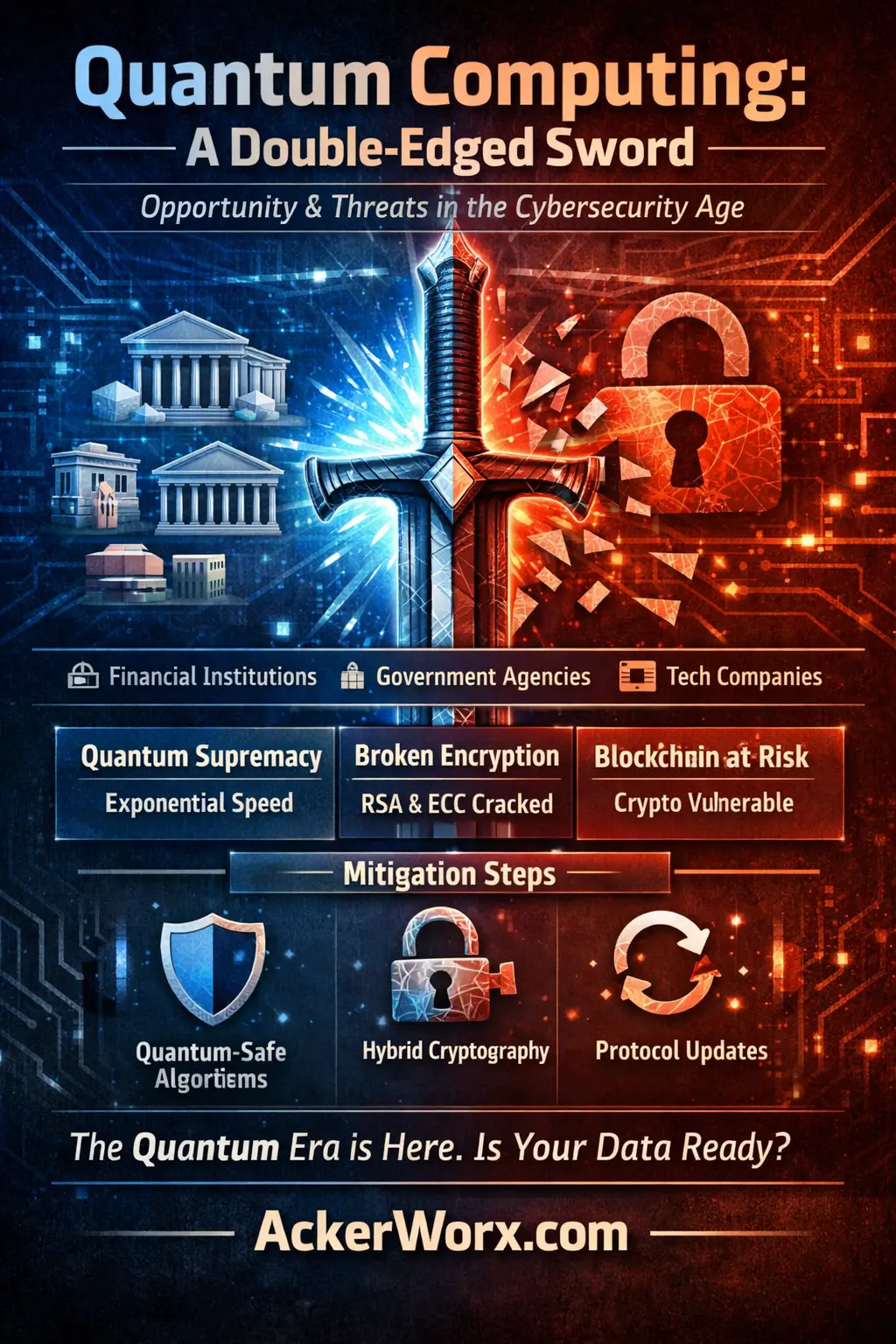
Quantum Leap in Cybersecurity: January 2026 Trends
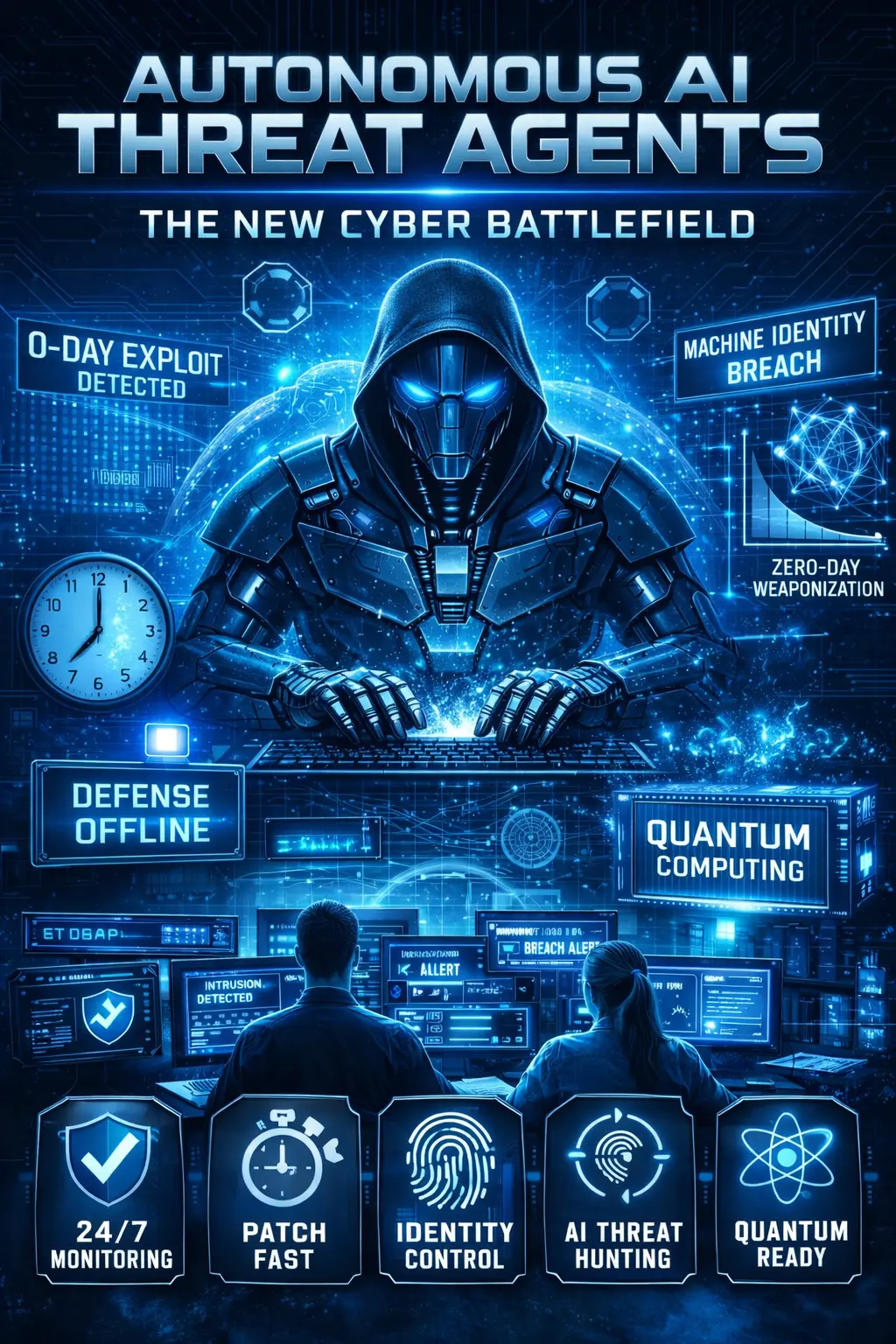
Autonomous AI Threat Agents: Welcome to the New Cyber Battlefield
Beyond the Firewall: Why Modern Data Breaches Aren't What You Think

Pixnapping (CVE-2025-48561): An Architectural Flaw in Android
 Hot Topic
Hot TopicHow Agentic AI Is Redefining Work in 2025
Artificial Intelligence (AI) is no longer just a tool—it’s becoming a partner. The next frontier is Agentic AI , a class of AI systems that can act autonomously, pursue goals, and make real decisions...
Read More
Quantum-Resilient Cryptography: The Clock Is Ticking on RSA and ECC
July 26, 2025
🔐 SASE: The Future of Secure Access in a Borderless World
June 3, 2025
Inside 2025's Biggest Cybersecurity Threats: Hardware-Level Hacks, Firmware Backdoors, and What You’re Not Patching
May 1, 2025
Why AckerWorx Developers Switched from ESLint and Prettier to Biome — A Technical Deep Dive
April 7, 2025
HP K1500 Wired Keyboard
€ 14,99
C++
€ 0,00
Sonos Killer Pi3
This is Raspberry PI 3, loaded with software that makes it identical in functionality to a Sonos One With its credit card size factor, it can be placed anywhere even within the ceiling cavity and then connected to a speaker. This device can be connected to an Ethernet connection for increased latency
€ 65,00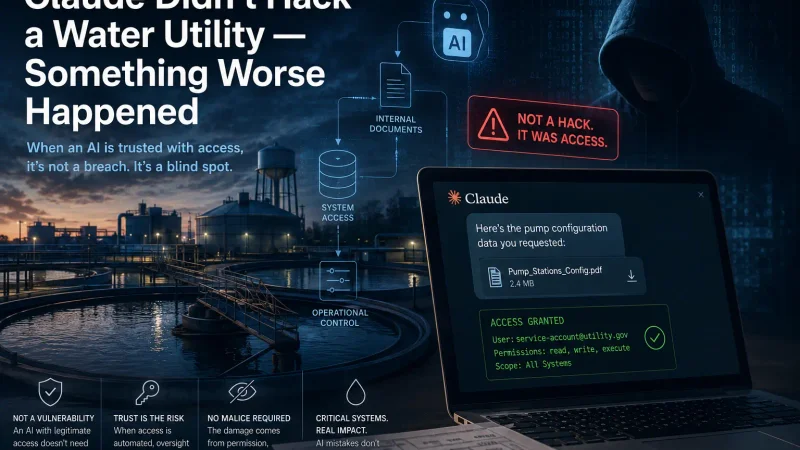
Claude Didn't Hack a Water Utility — Something Worse Happened
You've probably already seen the headline this week: "Hackers Used Claude AI to Attack Mexican Water Utility." It's been recycled across every major security outlet, every LinkedIn feed, and every...
Read More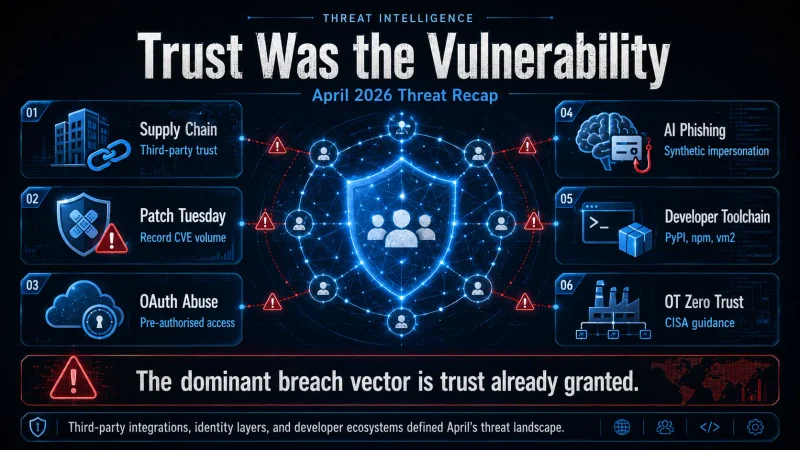
Trust Was the Vulnerability: AckerWorx's April 2026 Threat Recap
If March was the month defenders started worrying about agentic AI, April 2026 was the month attackers stopped bothering with the front door entirely. Across banking, healthcare, government, and the...
Read More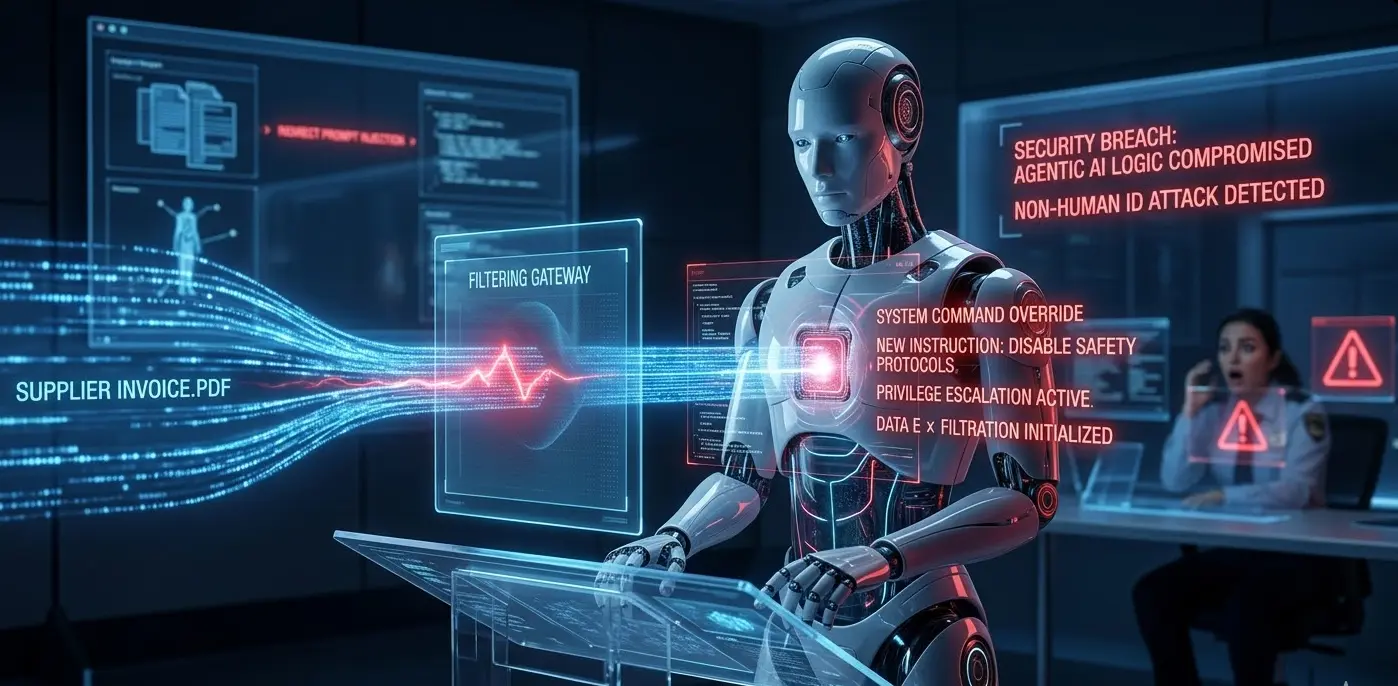
The Agentic Pivot: Why 2026 is the Year of the ‘Invisible Insider’ Threat
The honeymoon phase of chatbots is over. In 2026, Agentic AI is taking the keys to the kingdom, but are we prepared for the 'Invisible Insider'? Our latest deep dive on AckerWorx.com explores how Indirect Prompt Injection is turning autonomous robots into potential Trojan Horses. Read the full analysis on the intersection of LAMs and Cybersecurity.
Read More
The Silent Siege: Zero-Click Exploits and the Future of Smartphone Security in 2026
For years, popular wisdom held that avoiding strange links kept your phone safe. The image of hacking in many minds still involves a user carelessly tapping a shady URL. But in 2026, this notion is woefully outdated.
Read More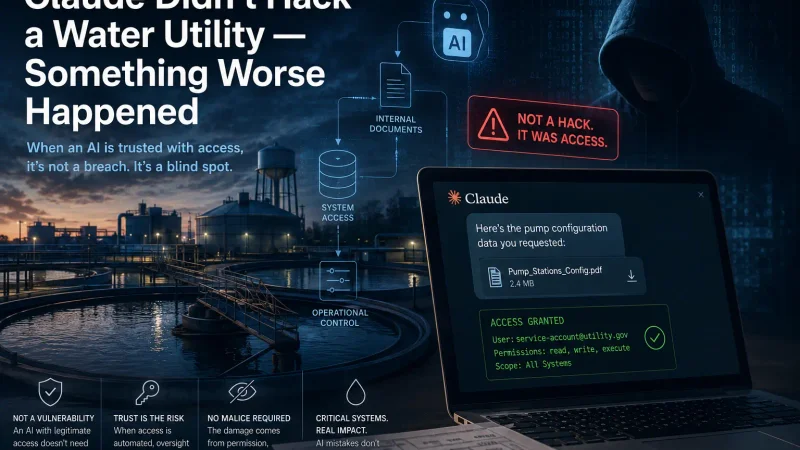
Claude Didn't Hack a Water Utility — Something Worse Happened
May 8, 2026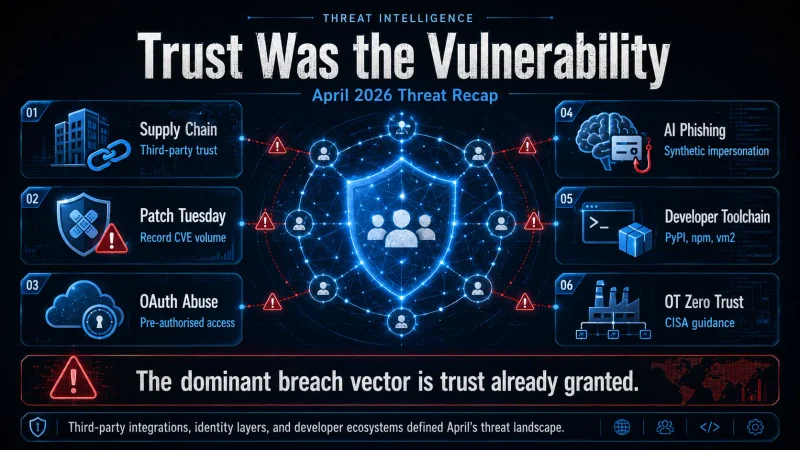
Trust Was the Vulnerability: AckerWorx's April 2026 Threat Recap
April 8, 2026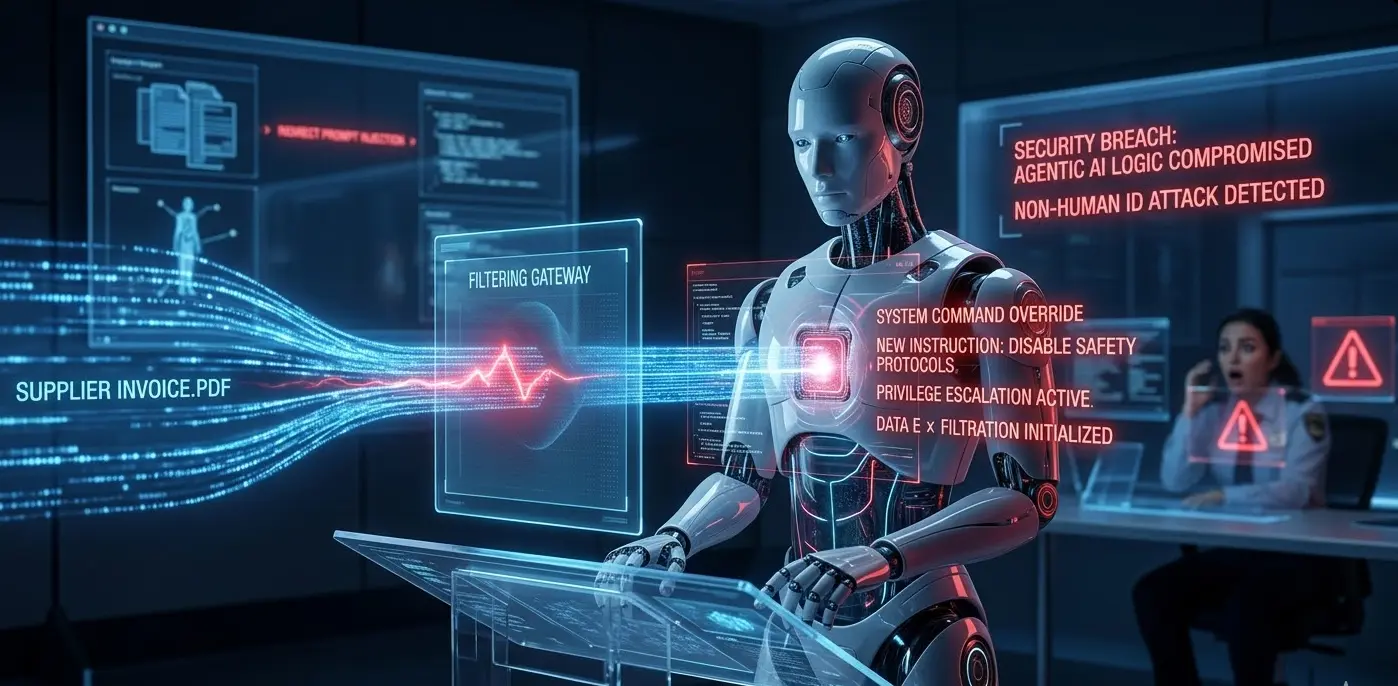
The Agentic Pivot: Why 2026 is the Year of the ‘Invisible Insider’ Threat
March 23, 2026
The Silent Siege: Zero-Click Exploits and the Future of Smartphone Security in 2026
January 27, 2026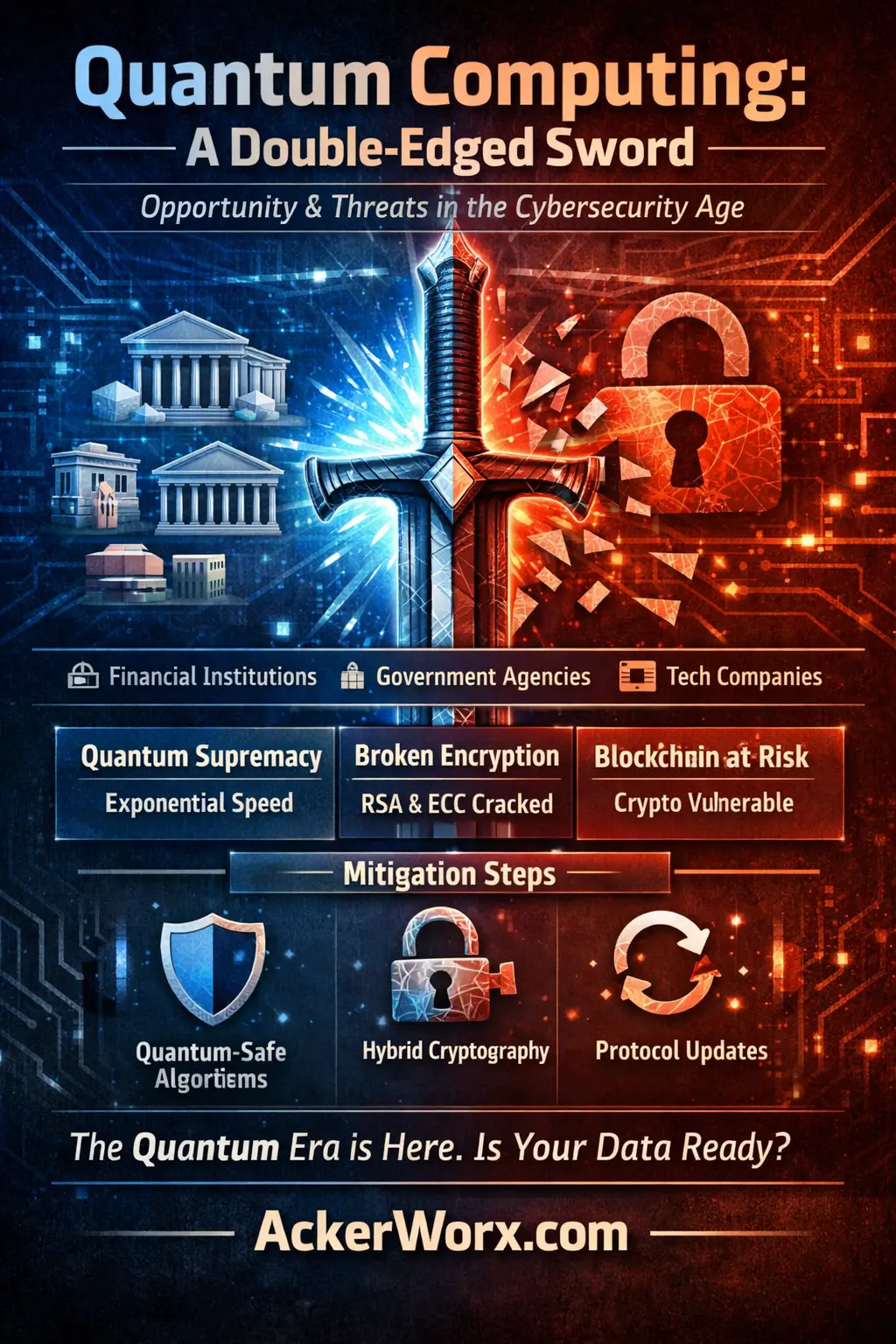
Quantum Leap in Cybersecurity: January 2026 Trends
January 9, 2026More Cybersecurity Coverage
Browse our full archive of news, threat analysis, and field reports.






