Elcomsoft iOS Forensic Toolkit
<section data-id="057c2f3" data-element_type="section" data-settings="{"_ha_eqh_enable":false}"> <div> <div> <div data-id="1817ce4" data-element_type="column"> <div> <div> <div data-id="0bb2db2" data-element_type="widget" data-widget_type="text-editor.default"> <div> <div> <b>Perform physical and logical acquisition of iPhone, iPad and iPod Touch devices. Image device file system, extract device secrets (passwords, encryption keys and protected data) and decrypt the file system image.</b> <div> <ul> <li>Physical acquisition for 64-bit iOS devices with or without a jailbreak</li> <li>Logical acquisition extracts backups, crash logs, media and shared files</li> <li>Unlocks iOS devices with pairing records (lockdown files)</li> <li>Extracts and decrypts protected keychain items</li> <li>Real-time file system acquisition</li> <li>Automatically disables screen lock for smooth, uninterrupted acquisition</li> </ul> </div> </div> </div> </div> </div> </div> </div> </div> </div> </section><section data-id="2126c8fe" data-element_type="section" data-settings="{"_ha_eqh_enable":false}"> <div> <div> <div data-id="38268bdf" data-element_type="column"> <div> <div> <div data-id="d0ca571" data-element_type="widget" data-widget_type="product-related.default"> <div><section> <div> <h2 data-fontsize="23" data-lineheight="34.5px"></h2> </div> </section></div> </div> </div> </div> </div> </div> </div> </section>
Categories:Software
Tag:Elcomsoft
Forensic Access to iPhone/iPad/iPod Devices running Apple iOS
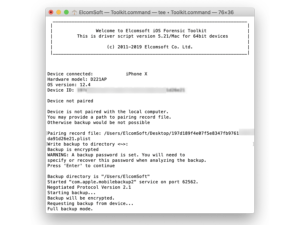
Perform the complete forensic acquisition of user data stored in iPhone/iPad/iPod devices. Elcomsoft iOS Forensic Toolkit allows imaging devices’ file systems, extracting device secrets (passcodes, passwords, and encryption keys) and accessing locked devices via lockdown records.
Physical Acquisition of iOS Devices
Physical acquisition is the only acquisition method to extract full application data, protected keychain items, downloaded messages and location history. Physical acquisition returns more information compared to logical acquisition due to direct low-level access to data. Elcomsoft iOS Forensic Toolkit supports jailbroken 64-bit devices (iPhone 5s and newer) running most versions of iOS 7 through 13.x. The use of a bootrom-based jailbreak enables partial file system & keychain acquisition for BFU, locked and disabled iPhone models ranging from the iPhone 5s through iPhone X (via checkra1n jailbreak). Full file system and complete keychain acquisition for unlocked devices from this device range.Full File System Extraction and Keychain Decryption Without a Jailbreak
A jailbreak-free extraction method based on direct access to the file system is available for a limited range of iOS devices. Using an in-house developed extraction tool, this acquisition method installs an extraction agent onto the device being acquired. The agent communicates with the expert’s computer, delivering robust performance and extremely high extraction speed topping 2.5 GB of data per minute. Better yet, agent-based extraction is completely safe as it neither modifies the system partition nor remounts the file system while performing automatic on-the-fly hashing of information being extracted. Agent-based extraction does not make any changes to user data, offering forensically sound extraction. Both the file system image and all keychain records are extracted and decrypted. The agent-based extraction method delivers solid performance and results in forensically sound extraction. Removing the agent from the device after the extraction takes one push of a button.